
February 2026 Cyber AB Town Hall Recap: DFARS Updates, Clarifying “Significant Changes,” and a Sharper Definition of What It Means to Protect CUI
February’s Cyber AB Town Hall had two distinct themes that matter for contractors operating within the Defense Industrial Base.
First, the program is getting more explicit about expectations that have always existed but were often treated as optional or “interpretive,” especially around CUI handling, scope discipline, and what happens when your assessed environment changes after certification or self-assessment.
Second, the ecosystem continues to scale. Level 2 certifications are climbing, assessor capacity keeps trending up, and the Cyber AB is building out the operational muscle needed to support what is still a very small slice of total expected demand.
Policy updates: DFARS changes and what they signal
The spotlight segment of the Town Hall was a deeper discussion of the Department of Defense’s recent DFARS updates and class deviation memoranda, presented by Regan Edens of the CMMC Industry Standards Council.
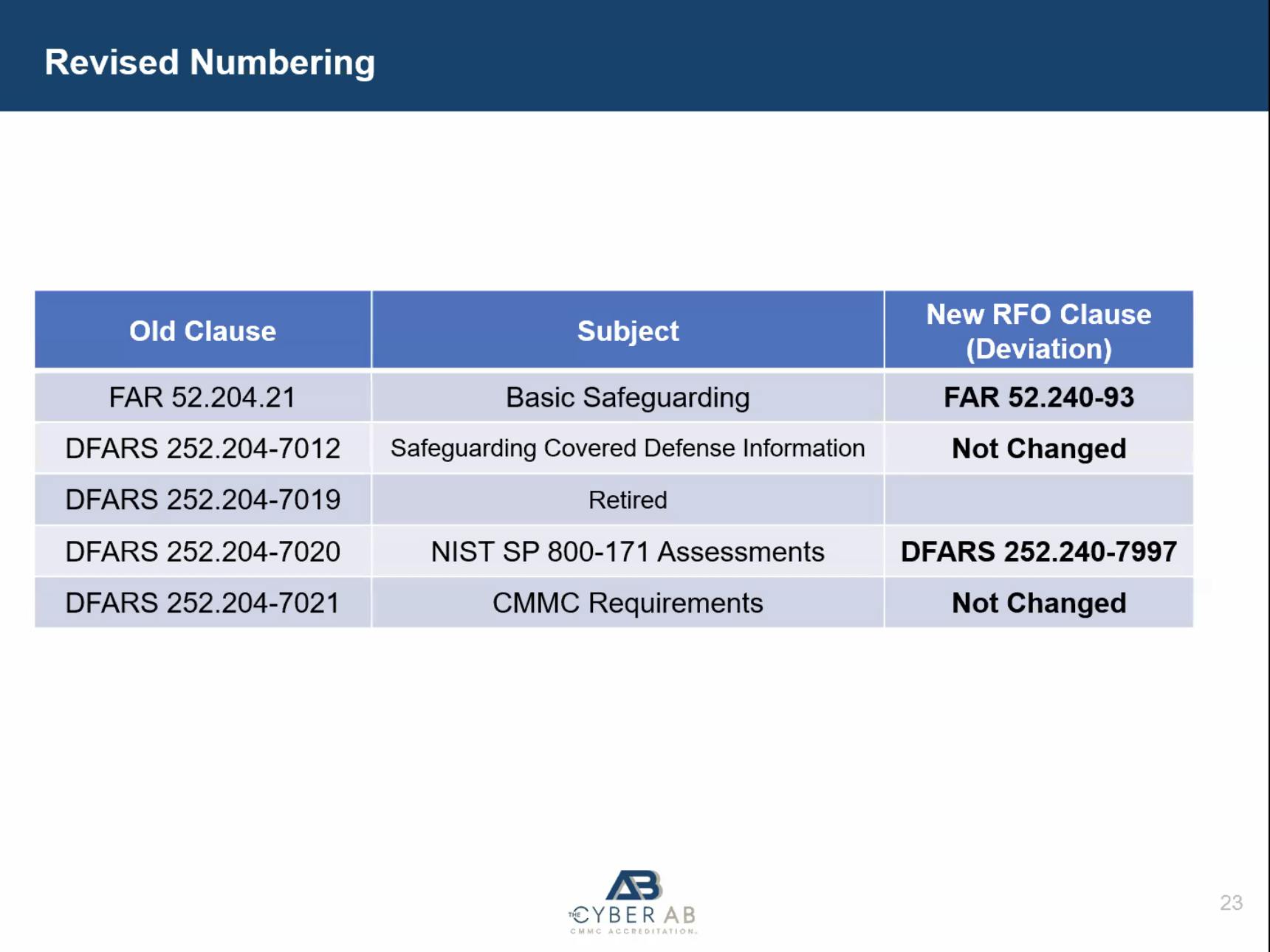
The key headline is that Phase 1 of the Revolutionary FAR Overhaul effort went into effect on February 1, 2026. From an ecosystem standpoint, this matters because it reorganizes and renumbers certain clauses and consolidates key cybersecurity requirements into a more coherent structure under DFARS Part 240.
The slide deck included a clause renumbering snapshot that many contractors will want to save, especially teams that track requirements by citation. In plain terms, some references are being reorganized, and at least one familiar clause number shifts. At the same time, not everything is changing. The most important takeaway is that contractors should pay close attention to how solicitations cite requirements going forward.
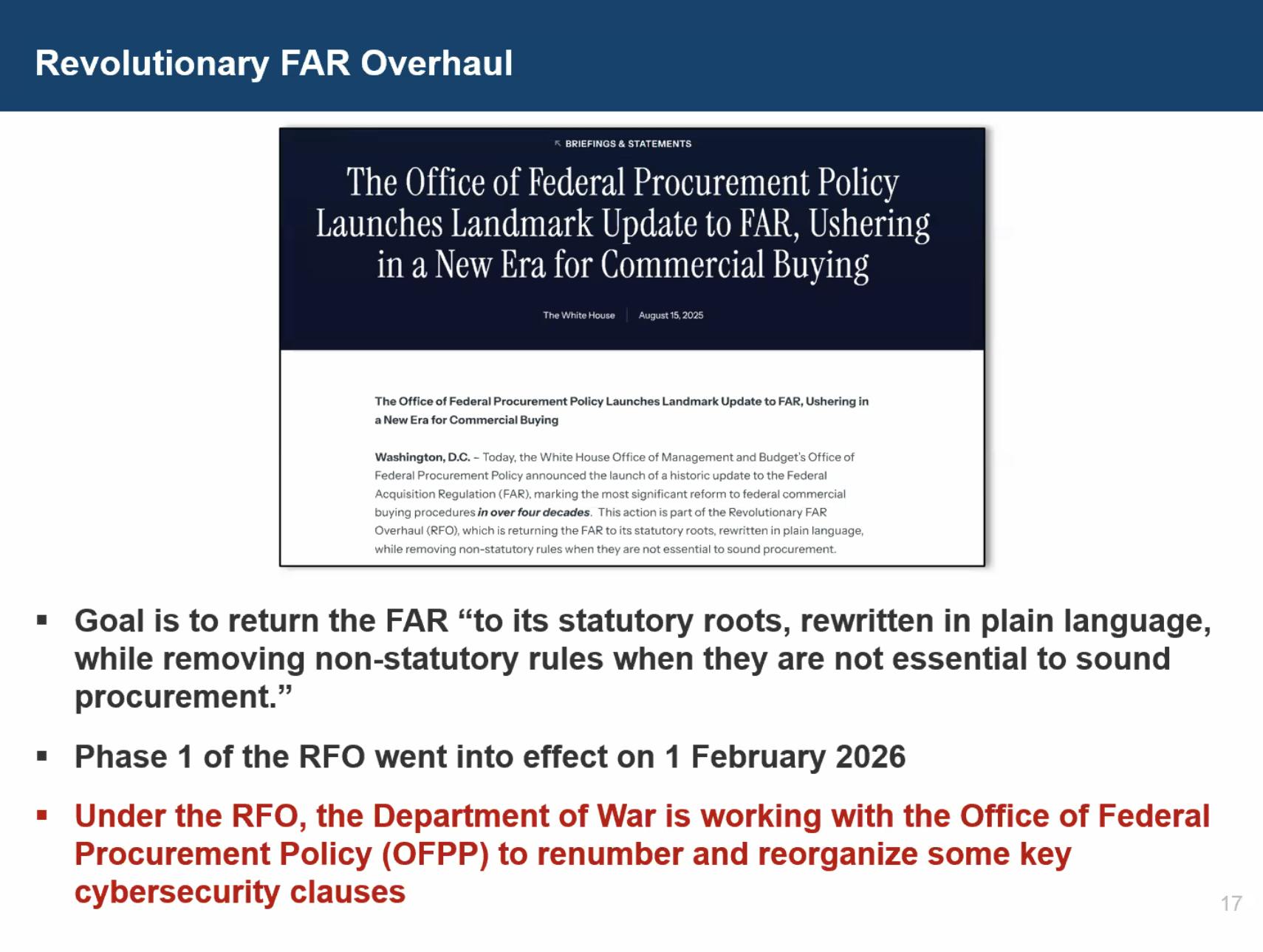
Edens’ larger point was not just that numbers changed. His argument was that the class deviation clarifies what has always been true about how to implement safeguarding requirements. The contract clause cannot be treated as a standalone cybersecurity checkbox. It must be implemented in the context of the federal CUI rule and DoD guidance that governs what CUI is, how it is identified and marked, and how it is safeguarded throughout the lifecycle of contract performance.
He emphasized that the memorandum explicitly reinforces alignment with the federal CUI program rule in 32 CFR Part 2002 and tightens expectations around identifying and safeguarding CUI, including controlled technical information. In other words, the Department is reducing the room for ambiguity that has led to persistent misunderstanding and bad advice across the market.
The practical takeaway for a typical DIB company is straightforward. This is a signal to get serious about CUI handling discipline now. Contractors that implement these requirements coherently today are less likely to face disruptive scope changes or reassessments later because they built an enclave or boundary story that was too narrow or not grounded in how CUI is actually handled.
A notable Q&A point involved OTAs. Edens clarified that DoD Instruction requirements around controlled technical information still apply in OTA environments. An OTA is not a free pass to ignore CUI protection obligations.
The Cyber AB also indicated that this topic will likely return in future webinars because the implications are significant and technical.
Understanding “significant changes” and how they can invalidate your assessment
One of the most useful sections of the Town Hall was the reset on what the program considers a “significant change” to an assessed environment.
Under 32 CFR, the integrity of an assessment is tied to the scope that was actually assessed. If that scope changes significantly, the assessment can be invalidated and a new assessment and affirmation may be required.
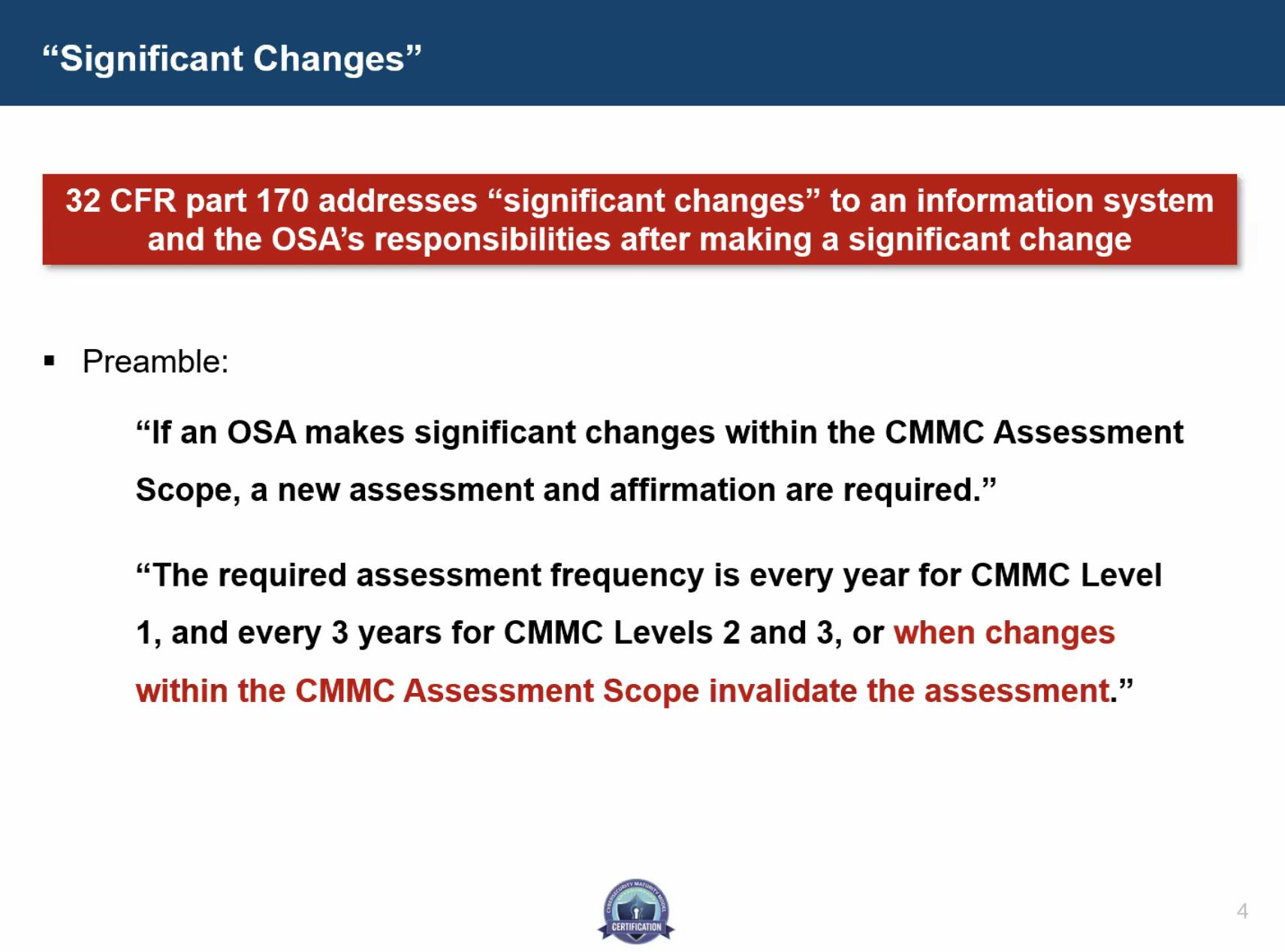
Matt Travis pointed to two existing sources of guidance: the 32 CFR preamble and the CMMC Level 2 Scoping Guide. The Scoping Guide highlights architectural or boundary changes such as network expansions or mergers and acquisitions that pull new environments into scope. It also draws a line between major boundary shifts and operational changes inside the existing boundary. Adding or subtracting resources within an established scope that still follow the existing SSP may not require a new assessment.
What makes this discussion important is ownership. The responsibility sits with the affirming official, defined in 32 CFR as the senior representative responsible for ensuring compliance with program requirements. That annual affirmation carries real risk. Travis explicitly connected this to False Claims exposure.
C3PAOs can offer a professional opinion on whether a change appears significant. They cannot provide recommendations during that discussion, and they are not the party on the hook for the affirmation. Accountability rests with the organization signing it.
If your environment evolves, you cannot treat CMMC as something you completed and moved on from. Scope decisions are governance decisions. Your SSP must reflect how your environment actually operates, not how it operated on assessment day.
Clarifying rules around C3PAO mock assessments
Travis also addressed mock assessments, formally called non-certification assessments under Section 3.4 of the Code of Professional Conduct.
Organizations can engage a C3PAO for a practice assessment before pursuing certification. However, if that same C3PAO later conducts the certification assessment, strict conditions apply. The mock assessment must follow formal procedures aligned with the CAP. It cannot include recommendations or consulting during the assessment itself. It must result in a formal deliverable documenting the results.
There are also limits on how assessments can be converted. A certification assessment can be paused and converted to a non-certification assessment. A mock assessment cannot simply be turned into an official certification midstream. A formal certification assessment must start cleanly.
These rules exist to protect impartiality, especially in a market where readiness and certification services are sometimes bundled aggressively.
Ecosystem update: Level 2 certifications continue to climb
The Town Hall also shared updated ecosystem metrics.
There are now 896 final Level 2 Certificates of CMMC Status issued, along with 36 conditional certificates and 110 Level 2 assessments currently in progress.
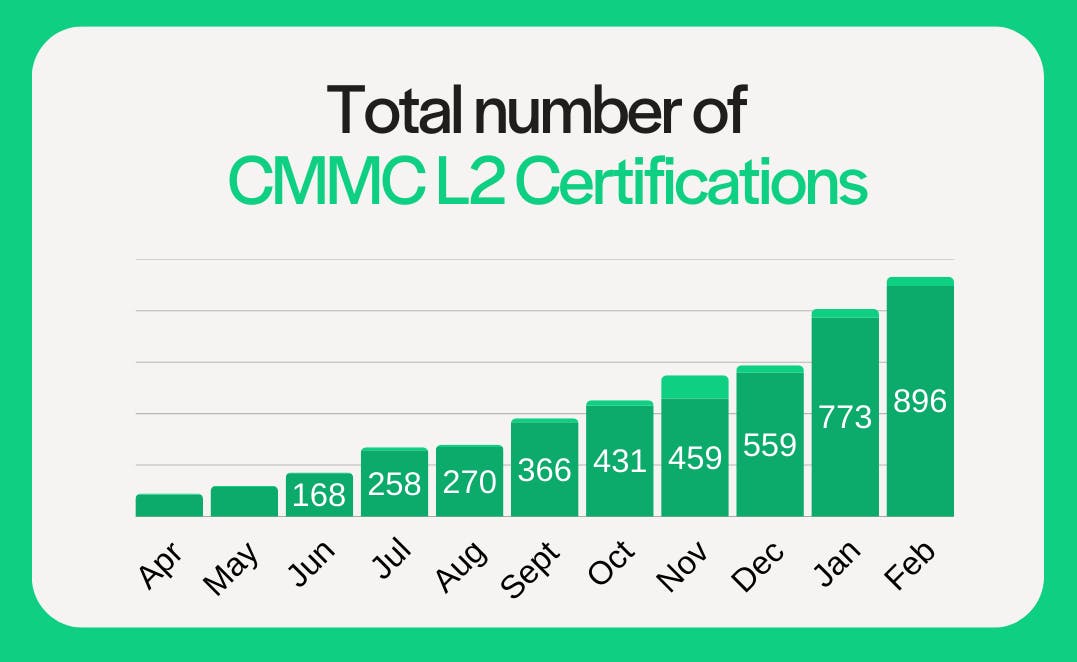
Authorized C3PAOs increased to 98. CMMC Certified Assessors rose to 748. Certified CMMC Professionals increased to 1,494, and Lead CCAs climbed to 452. Registered Practitioners and RPO participation also ticked upward, with RPOs at 378.
If you’re early in your journey, this reinforces a practical point. You don’t need to do this alone. The Marketplace exists for a reason, and the growth in RPOs and practitioners reflects where many organizations are finding structured support.
Accreditation timelines
Two Q&A threads stood out.
First, on C3PAO accreditation timelines, authorized C3PAOs have 27 months before accreditation is required under 32 CFR. Initial authorization lasts 13 months, after which a C3PAO can pursue reauthorization for the remaining time or enter the accreditation program. After month 27, authorized-only status is no longer sufficient to conduct assessments.
Second, CAP revisions are underway but not imminent. The committee reviewing updates is meeting multiple times per week, with hopes of internal review by the end of March. Realistically, broader ecosystem updates may land later this summer after coordination with the PMO and DIBCAC.
Additional CMMC program and ecosystem updates
The Town Hall also covered several operational updates across the broader CMMC ecosystem.
For C3PAOs, accreditation timelines were clarified again. Under 32 CFR, authorized C3PAOs have 27 months before accreditation becomes mandatory. Initial authorization lasts 13 months, after which a C3PAO can either pursue reauthorization for the remaining period or enter the accreditation program. After month 27, authorized-only status is no longer sufficient to conduct assessments. In parallel, work continues on updates to the CMMC Assessment Process (CAP). The review committee is meeting frequently, with hopes of internal review this spring and broader ecosystem updates potentially landing later this summer following coordination with the PMO and DIBCAC.
On the credentialing side, the transition of the CAICO function to ISACA is underway. Exams for CCP and CCA candidates are moving to PSI. Candidates don’t need to delay testing unless they prefer to wait for the new platform, and the underlying exam content is expected to remain largely the same. Measured Learning will stop allowing exam scheduling past March 15 to support the transition. Current credential holders won’t be required to recertify simply because administration is shifting to ISACA. Additional guidance is expected through upcoming webinars and at industry events.
There was also a practical reminder regarding Tier 3 background investigations. If your organization has a facility security clearance and a Facility Security Officer, the FSO may be able to contact your DCSA representative to inquire about investigation status before the six-month mark. Otherwise, the existing guidance remains to wait six months before requesting PMO assistance.
Finally, the Cyber AB confirmed there is no reduction in staffing related to the CAICO transition. The support routing model continues to run through the updated Support Request Form on the Cyber AB website, and the event calendar has been refreshed, including details for CS5 West in April.
Key takeaways from February's Town Hall
The consistent message from February’s Town Hall is that expectations are becoming more explicit, particularly around CUI handling and scope discipline.
If you’re preparing for Level 2, don’t treat scope as something you define once and forget. Revisit how you identify CUI. Confirm that your boundary reflects real data flows. Make sure your SSP matches how your environment actually operates.
If you’re tracking DFARS changes, understand that reorganizing clauses does not reduce safeguarding obligations. In many cases, it makes those obligations harder to sidestep.
And if you’re engaging readiness services, understand the difference between consulting and formal assessment.
We’ll continue to track updates and insights from each CyberAB Town Hall. For ongoing coverage, check out past recaps in the CMMC.com newsroom.