
The Myth of CMMC Waivers: Why “Wait and See” Is No Longer a Viable Strategy for DIB Organizations
As CMMC enforcement continues to ramp and requirements show up in real contracts and solicitations, one misconception continues to circulate across the Defense Industrial Base: that waivers will provide some organizations an “out” from CMMC certification requirements.
The truth for most DIB organizations? They won’t.
In a recent supplier communication, Northrop Grumman made their own and the government’s position unmistakably clear:
"Neither contracting officers nor prime contractors may waive or deviate from CMMC cybersecurity control and assessment requirements. Contracting officers may not award contracts to noncompliant contractors, and prime contractors may not award purchase orders to noncompliant subcontractors."
This message reflects what the Department of Defense has been signaling consistently through regulation, policy memoranda, and acquisition guidance: CMMC waivers are not a workaround, a delay tactic, or a substitute for certification. They are rare, tightly controlled exceptions intended only for mission-critical circumstances.
For contractors still hoping waivers will preserve their contract-eligibility without CMMC certification, this is a wake-up call.
What CMMC waivers actually do (and do not)
CMMC waivers allow senior DoD acquisition officials to exclude or reduce CMMC Level 2 or Level 3 third-party assessment requirements for a specific procurement or class of procurements, under very limited conditions.
They do not:
- Apply to types of companies broadly
- Remove underlying cybersecurity obligations
- Provide long-term exemption from certification
- Allow primes to bypass flowdown requirements
Waivers are contract-specific, time-bound, and approved only at the highest levels of the Department. Even when granted, contractors remain responsible for complying with applicable FAR, DFARS, and NIST requirements for protecting FCI and CUI.
In other words: a waiver may delay when or if a CMMC third-party assessment is required, but not whether the underlying security obligations apply.
When CMMC waivers may be considered
DoD guidance clarifies that waivers are only contemplated in narrow scenarios, such as when:
- Market research shows certification requirements would significantly delay delivery of a mission-critical capability
- The government is seeking competition from non-traditional defense suppliers
Even then, waiver requests must be coordinated through the Component CIO, approved by a Service or Component Acquisition Executive, supported by a mitigation plan, and reported quarterly to senior DoD leadership.
They are not discretionary decisions made by contracting officers or prime contractors in response to supplier readiness gaps.
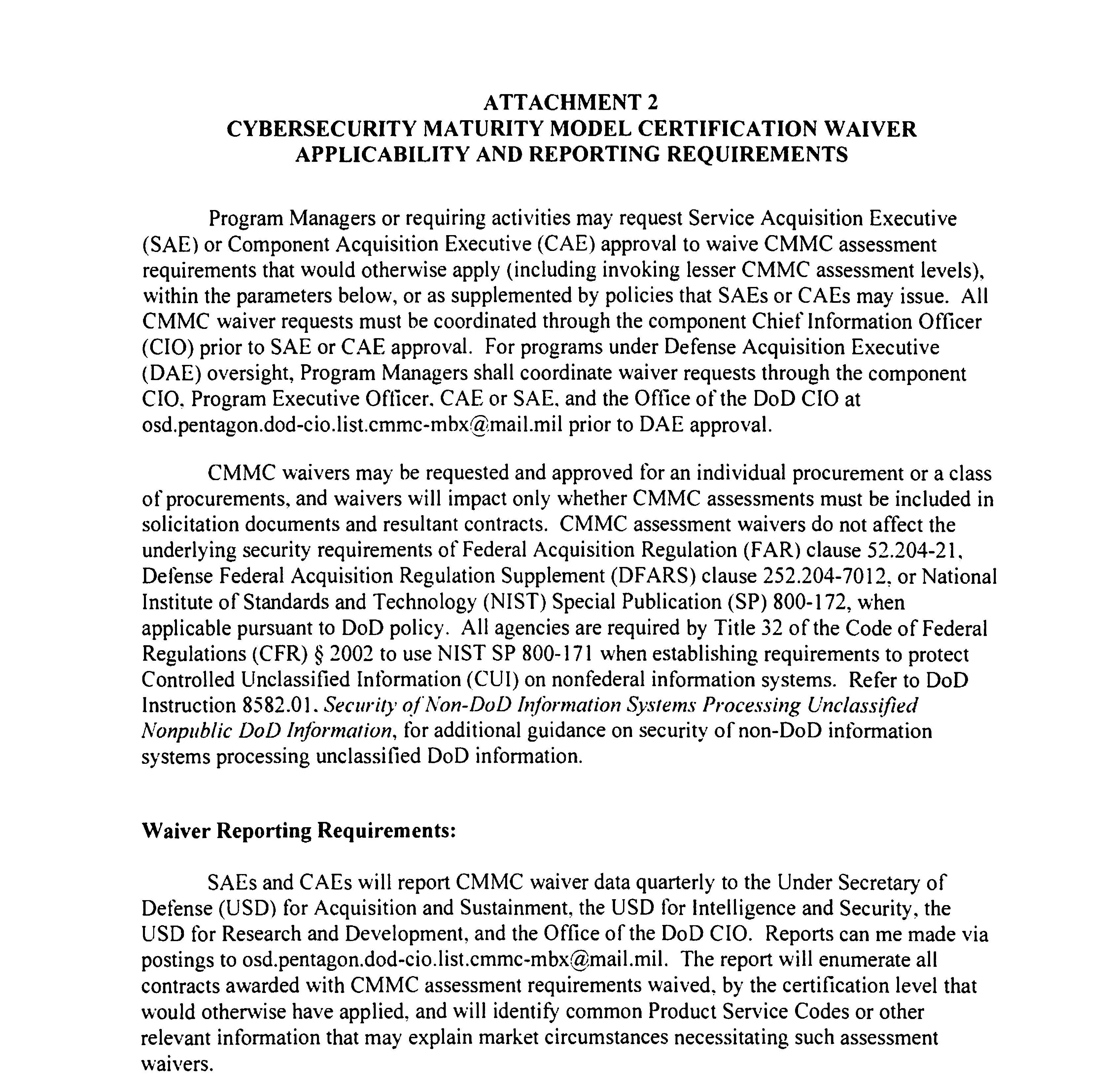
Image source: DoD's Implementing the Cybersecurity Maturity Model Certification (CMMC) Program memo
When CMMC waivers are effectively off the table
DoD policy also makes clear where waivers are unlikely or inappropriate, including:
- Level 1 contracts
- Level 2 contracts requiring self-assessments
- Level 2 work performed by cleared defense contractors
- Level 3 programs or contracts involving access to classified information
For most contractors handling FCI or CUI, the Department’s expectation is straightforward: CMMC certification is required.
Why “waiver chasing” fails as a strategy
The reason waivers are so limited is structural, not procedural.
CMMC represents a deliberate shift away from self-attestation toward verifiable, consistent cybersecurity baselines across the defense supply chain. Broad or frequent waivers would undermine the very objective of the program.
From the government’s perspective, granting a waiver is not a concession to industry. It is an explicit acceptance of risk to national security. That is why each waiver requires justification, mitigation, executive approval, and reporting.
This also explains why assumptions that large primes will “lobby for waivers” are misplaced. The oversight and accountability mechanisms built into CMMC make waivers a high-risk option for acquisition executives, not a convenience.
In reality, many large primes have been enforcing CMMC in their own supply chains well ahead of the government’s phased rollout. Supplier questionnaires and formal communications from primes such as RTX, Lockheed Martin, and Boeing have made it clear that Level 2 (C3PAO) certification (or at least readiness) is the baseline expectation. For DIB organizations, “wait and see” is no longer a viable strategy, if it ever was.
The bottom line for DIB organizations: CMMC is unavoidable
CMMC waivers exist, but they are not a safety net for unprepared contractors.
They are narrow, temporary tools used to protect mission execution, not business models. They do not eliminate security obligations, they do not follow companies from contract to contract, and they do not replace certification as the new baseline for defense work.
For organizations planning to compete in the defense market over the next several years, the conclusion is unavoidable:
CMMC readiness is no longer optional, and waiting for a waiver is not a strategy.